Author: Emin YÖNEY | Senior Solution Consultant
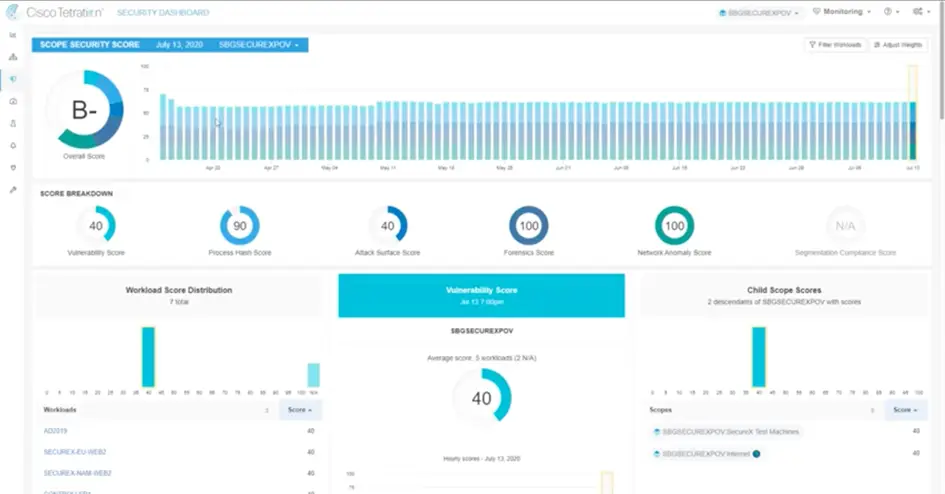
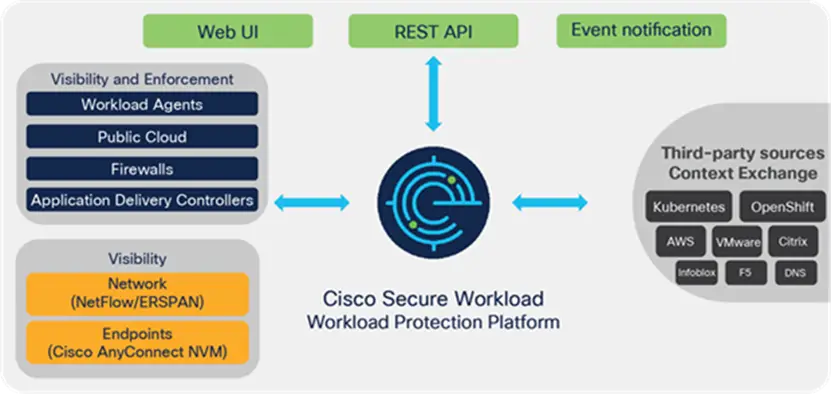
Cisco Secure Workload (Tetration) is a network security and analysis platform. This platform allows you to detect any threats on your network by analyzing real-time traffic on your corporate networks.
It monitors applications, processes, users, and devices on your network and helps understand their relationships so you can be alerted immediately if any threats come to your network.
It also tracks where applications on your network are running and what resources they are using, so you can identify performance issues.
Cisco Secure Work Load (Tetration) also supports cloud-native applications, so you can monitor all applications in your enterprise network and understand the relationships between different platforms.
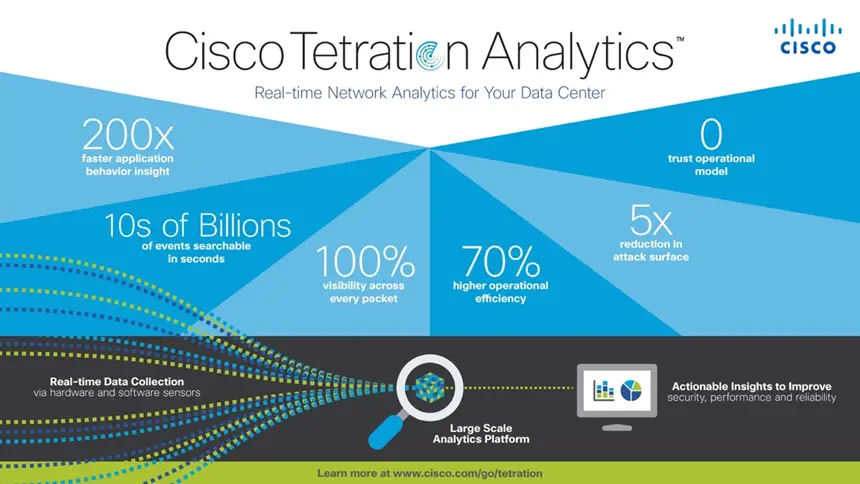
The main features offered by the application in network security and analysis are as follows.
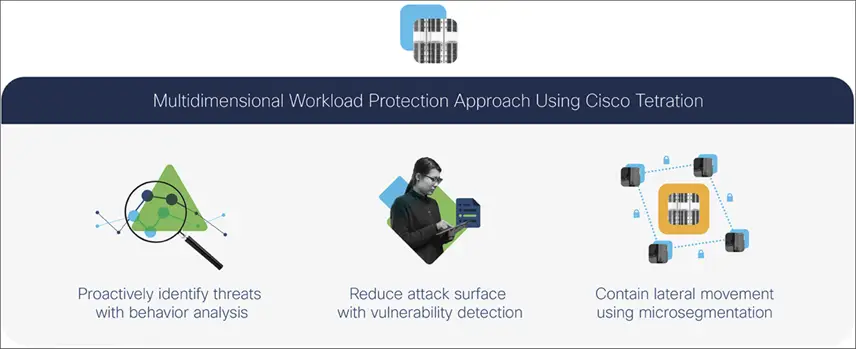
- Secure Workload’s (Tetration) automated approach helps in rapid deployment of Microsegmentation.
- Zero Trust in the Micro Segmentation application model enables you to implement Micro Segmentation.
- It quickly detects threats in the network by performing real-time traffic analysis.
- Relationship mapping helps to understand the relationships between application, process, user and device.
- It detects performance issues and optimizes resources by monitoring resource usage.
- It is compatible with and supports applications running on popular cloud-based application services such as AWS, Microsoft Azure, and Google Cloud Platform. It also supports applications running in your own private cloud environment.
- Monitors application performance and detects performance issues.
- It detects malicious content by performing content inspection.
- Provides useful information for the business by analyzing data.
- It summarizes the data and presents it in an understandable way.
- Automatically manages and edits policies.
- Detects malware on your network.
To summarize, Cisco Secure Workload (Tetration) is a groundbreaking platform in network security and analytics. It monitors all applications, processes, users, and devices on your network, allowing you to detect any threats and troubleshoot performance issues.